Have you ever spent a night manually rotating database passwords because they were about to expire? Or discovered that access credentials were stored in plain text inside a config file running across ten servers?
These situations are more common than you’d think, and they represent one of the most underestimated security risks in modern cloud infrastructures.
Amazon Web Services offers an elegant solution to this problem: IAM authentication for Aurora PostgreSQL and Amazon RDS. Instead of static passwords — which need to be managed, rotated, and protected — you use temporary tokens generated on the fly at connection time. No password to store, no secret to pass around in config files.
In this article we’ll look at how it works, how to configure it, and when it actually makes sense to use it.
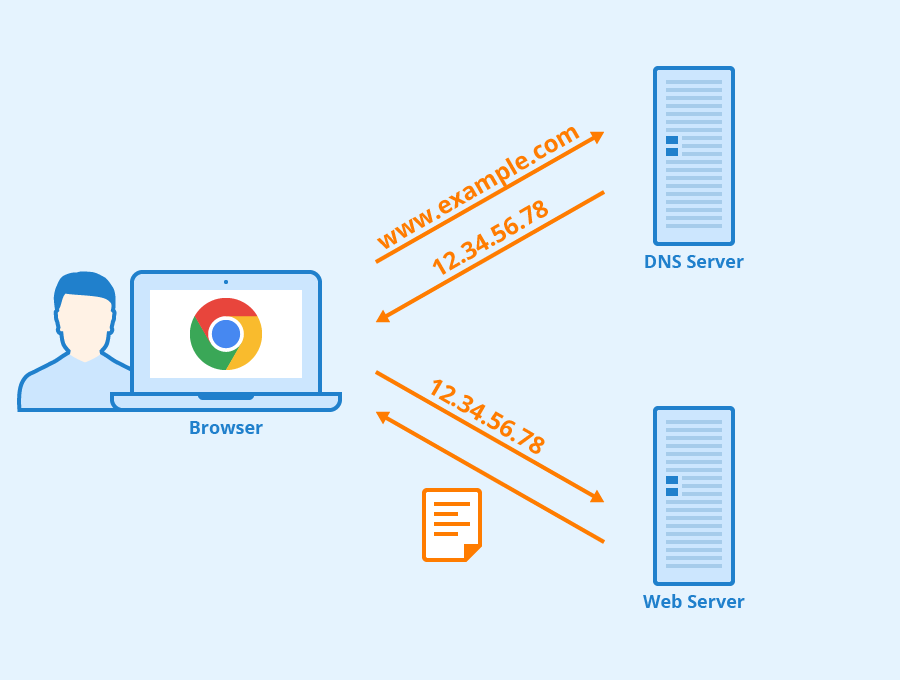
How IAM Authentication Works
The idea is straightforward: instead of requiring a fixed password, the database accepts a temporary token generated on demand, with a very short lifespan — around 15 minutes.
The process works in three steps:
- The application (or user) holds an IAM identity with the correct permissions
- A digitally signed temporary token is requested from AWS
- The token is used as the password to connect to the database
The token is generated using the AWS CLI:
aws rds generate-db-auth-token \
--hostname my-cluster.cluster-abc123.eu-west-1.rds.amazonaws.com \
--port 5432 \
--region eu-west-1 \
--username my-userThe result is a long digitally signed string. It expires after 15 minutes, so even if intercepted it would be completely useless almost immediately.
Configuring the Aurora Cluster
First, you need to enable IAM authentication on the cluster. It’s not active by default — it must be explicitly enabled in the Aurora cluster settings, either from the AWS console, via Terraform, or through the CLI.
Once enabled, create the PostgreSQL user and assign it the special rds_iam role, which tells the system to accept IAM tokens instead of passwords:
-- Create the user (name must match exactly what's in the IAM policy)
CREATE USER "mario.rossi@example.com";
-- Assign the IAM role
GRANT rds_iam TO "mario.rossi@example.com";Important: the PostgreSQL username must match exactly what is defined in the IAM policy and used when generating the token. Even a single uppercase/lowercase difference will cause an access error.
Creating the IAM Policy
Access won’t work until you explicitly authorize the IAM identity to connect. The policy must grant the rds-db:connect action on the specific cluster resource.
The resource ARN follows this pattern:
arn:aws:rds-db:REGION:ACCOUNT-ID:dbuser:RESOURCE-ID/USERNAMEFull example policy in JSON:
{
"Version": "2012-10-17",
"Statement": [{
"Effect": "Allow",
"Action": "rds-db:connect",
"Resource": "arn:aws:rds-db:eu-west-1:123456789012:dbuser:cluster-ABC123/mario.rossi@example.com"
}]
}How do you find the resource-id? It’s not the cluster name — it’s an internal identifier. You can find it in the RDS console under Configuration → Resource ID, or via CLI:
aws rds describe-db-clusters \
--query 'DBClusters[*].[DBClusterIdentifier,DbClusterResourceId]'Connecting to the Database
With the policy and user configured, the connection flow is as follows:
- Generate the token with
aws rds generate-db-auth-token - Use the token as the
passwordvalue in the connection string - Make sure SSL is enabled (it’s mandatory with IAM auth)
Example with psql:
TOKEN=$(aws rds generate-db-auth-token \
--hostname my-cluster.cluster-abc123.eu-west-1.rds.amazonaws.com \
--port 5432 --region eu-west-1 --username mario.rossi@example.com)
psql "host=my-cluster.cluster-abc123.eu-west-1.rds.amazonaws.com \
port=5432 sslmode=require \
dbname=my_database \
user=mario.rossi@example.com \
password=$TOKEN"Example with Python and psycopg2:
import boto3
import psycopg2
client = boto3.client('rds', region_name='eu-west-1')
token = client.generate_db_auth_token(
DBHostname='my-cluster.cluster-abc123.eu-west-1.rds.amazonaws.com',
Port=5432,
DBUsername='mario.rossi@example.com'
)
conn = psycopg2.connect(
host='my-cluster.cluster-abc123.eu-west-1.rds.amazonaws.com',
port=5432,
database='my_database',
user='mario.rossi@example.com',
password=token,
sslmode='require'
)Why It’s Worth Using
Concrete benefits compared to traditional password management:
- No passwords to manage or rotate: the token expires on its own after 15 minutes
- Centralized access control: whoever has the IAM permission can connect — everyone else is automatically blocked
- Audit trail: every access is traceable in CloudTrail
- Easy revocation: just remove the IAM policy to block access instantly
- Works with IAM roles: perfect for EC2, Lambda, and ECS containers with no hard-coded secrets
Limitations to Keep in Mind
- Short-lived tokens: applications that maintain persistent connections need to handle token renewal before expiry
- AWS dependency: the client must be able to reach the AWS endpoint to generate the token — it won’t work offline or in isolated environments
- Maximum 200 IAM connections per database: keep this limit in mind for high-concurrency architectures
- SSL required: if your infrastructure has SSL constraints, factor this in
When It Makes Sense to Use It
IAM authentication is the right choice when:
- You’re working in a cloud-native environment on AWS
- You want to eliminate static passwords from your stack
- You have users or services with temporary access needs (operators, CI/CD pipelines, Lambda functions)
- You’re building microservice architectures where each service has its own IAM role
It’s less suitable for legacy applications that don’t support automatic token renewal, or when operating in hybrid environments with limited connectivity to AWS.
Conclusion
Database password management is one of those problems that tends to get pushed back until it becomes urgent — usually at the worst possible moment. IAM authentication doesn’t solve everything, but it eliminates an entire category of risk without adding significant operational complexity.
In a modern AWS architecture, where every component already has its own IAM role, enabling it is often the most natural choice: no secret manager to configure, no rotation to schedule, no password to protect.
If you’re building something new on Aurora or RDS, it’s worth starting with IAM authentication from day one. Adding it later to existing systems takes considerably more effort than it might seem.





Lascia un commento